As of June 2021, Microsoft has confirmed TPM 2.0 support will be required to install Windows 11. So what does this mean for the enterprise users?
What is a TPM?
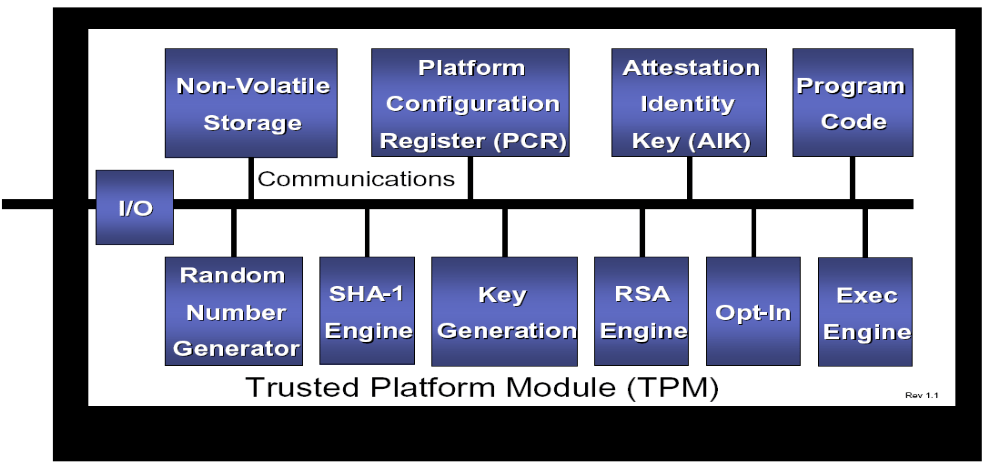
A TPM or “Trusted Platform Module” is a dedicated piece of hardware with the capability to generate and store encryption keys; as well as perform cryptographic functions in a tamper-resistant manner. TPM’s have been common on major mobile devices for the past few years. Apple’s Secure Enclave and Google’s Titan M chip are both proprietary variants of a TPM.
How does a TPM work?
A TPM generates and stores cryptographic keys as a separate hardware entity on a device outside of the main disk/storage. This prevents an attacker from gaining access to private keys and other sensitive data even if the device’s operating system is compromised. TPM’s also safeguard data if an attacker attempts to bypass encryption to access the disk contents even if they were to remove the TPM chip or try to access the disk on another device. The TPM is manufactured with a key pair (private/public) built into the hardware, called the endorsement key (EK). The EK is unique to a particular TPM and is signed by a trusted Certification Authority (CA). This manufacturing practice further prevents tampering and can also be used to establish trust as well as be used as a form of non-repudiation.
Figure 1 Example of TPM architecture. Source: https://courses.cs.washington.edu/courses/csep590/06wi/finalprojects/bare.pdf J. Christopher Bare
While a TPM has been required for OEM’s to achieve Windows Certification, this is the first time a compatible TPM has been required for Windows to be installed. Microsoft claims that a combination of their latest security features: Windows Hello, Device Encryption, virtualization-based security, hypervisor-protected code integrity (HVCI) and Secure Boot “have been shown to reduce malware by 60 percent.” With the current rise of Ransomware and user credential abuse, Microsoft believes the utilization of a TPM will significantly damper this threat.
How to Check a Device for Windows 11 Compatibility
One method of checking the state of a Windows device TPM:
- Open a run prompt
- Type “tpm.msc” and click Ok
- You will then be presented with the TPM status of the device
Microsoft plans to offer a PC Health Check Tool to check for Windows 11 compatibility and will be available at https://www.microsoft.com/en-us/windows/windows-11#pchealthcheck (coming soon at time of writing).
Overview:
The new security requirements for Microsoft’s newest operating system seems to be a big push to raise the security posture of the modern enterprise. Microsoft Windows is the de facto operating system for billions of corporate assets all over the world. Applying more stringent hardware-based security for Windows seems to be the method Microsoft has chosen to combat credential harvesting and ransomware attacks that have been on the rise.
Additional requirements:
- A UEFI BIOS (firmware) will be required to utilize TPM 2.0 and all legacy options such as “CSM” must be disabled.
- Among the TPM 2.0 requirement of Windows 11 is also the validation of new hardware. Only Intel 8th-gen and newer, as well as Zen 2 AMD architecture are officially supported. Since support relies on in house validation done at Microsoft; it is possible older hardware will be added to the support list.
- TPM functionality has been baked into most major hardware vendors at the firmware level since 2015. Thus, it is unlikely a TPM will have to be added to most enterprise machines.
About Schneider Downs Cybersecurity
The Schneider Downs cybersecurity practice consists of experts offering a comprehensive set of information technology security services, including penetration testing, intrusion prevention/detection review, ransomware security, vulnerability assessments and a robust digital forensics and incident response team. For more information, visit www.schneiderdowns.com/cybersecurity or contact the team at [email protected].
In addition, our Digital Forensics and Incident Response teams are available 24x7x365 at 1-800-993-8937 if you suspect or are experiencing a network incident of any kind.